Dependency injection (DI) is a powerful software design pattern that promotes modularity and testability. Mastering dependency injection modules takes your development skills to the next level, enabling you to build robust and maintainable applications. These modules act as centralized hubs for managing dependencies, simplifying the process of injecting required objects into classes and components.
By effectively utilizing DI modules, you can:
* Decrease code duplication and improve code reusability.
* Boost the testability of your application by decoupling classes from concrete implementations.
* Promote loose coupling between components, making it easier to modify and extend your application.
To truly master DI modules, delve into their configuration options, explore advanced techniques like dependency resolution strategies, and learn how to implement custom module resolvers for specific needs.
Building Robust Applications with Modular Design Patterns
Crafting resilient applications in today's fast-paced technological landscape demands a strategic approach. Utilizing modular design patterns emerges as a cornerstone for constructing adaptable software architectures that can withstand the test of time. By fragmenting applications into self-contained modules, developers facilitate code reusability, streamline maintenance processes, and minimize the impact of changes.
- Moreover, modular design patterns cultivate collaboration among development teams by encapsulating functionality within well-defined boundaries. This paradigm drastically minimizes the risk of unforeseen interactions between disparate components, culminating in a more solid overall system.
- Consequently, embracing modular design patterns is an essential practice for constructing applications that are not only operative but also sustainable.
Unlocking Code Flexibility: Exploring Injection Module Concepts
Injection modules provide a potent paradigm for enhancing the adaptability and extensibility of software applications. By seperating core functionalities from peripheral tasks, these modules facilitate developers to integrate specialized behaviors on demand. This modular architecture fosters a more flexible and maintainable codebase, paving the way for seamless evolution to evolving requirements.
- Injection modules often involve a framework that handles the registration and invocation of components.
- Engineers can specify reusable modules with specific functionalities, thereby promoting code reuse and composability.
- Exploiting injection modules streamlines the development process by facilitating a structured approach to code design.
Secure Programming Practices for Key Handling
In today's interconnected world, robust key management is paramount. Applications increasingly rely on sensitive data encryption and access control mechanisms, making the implementation of secure programming practices essential. Developers must comprehend the intricacies of cryptography and implement best practices to safeguard cryptographic keys throughout their entire lifecycle. This involves strategies such as key generation, storage, distribution, rotation, and revocation. By embracing these principles, developers can mitigate risks associated with unauthorized access, data breaches, and malicious actors.
- Additionally, secure coding practices help prevent vulnerabilities that could be exploited to steal or misuse cryptographic keys.
- Regularly auditing and penetration testing are crucial to identify weaknesses in key management systems.
Ultimately, a holistic approach to cryptographic security requires a combination of strong technical foundations, secure coding practices, and continuous vigilance.
Secure Key Injection Strategies for Modern Applications
Modern applications require robust security measures to ensure sensitive data from untrusted actors. One fundamental aspect of this is secure key injection, the process of implementing cryptographic keys into applications in a reliable manner. Breaches related to key injection can severely compromise application security, leading to data exposure. To mitigate these risks, developers must adopt secure key injection strategies that leverage best practices for secure storage.
- Consider hardware-based security modules (HSMs) for storing and generating cryptographic keys.
- Utilize strong access controls and authorization mechanisms to control access to sensitive keys.
- Encrypt keys both in transit and at rest, using industry-standard encryption algorithms.
- Periodically audit and monitor key management practices to identify potential vulnerabilities.
Effective Implementation of Injection Modules in Software Development
Injecting modules into software applications provides a powerful mechanism for enhancing functionality without tampering the core application logic. A efficient injection module can seamlessly integrate into an existing software architecture, promoting modularity and maintainability.
To ensure effective implementation, developers should focus on a defined module interface, adhering to established conventions. This strengthens code readability and facilitates the process of developing new modules. Additionally, thorough testing of injected modules is essential to avoid potential errors that could compromise the overall application stability.
- Utilize dependency injection frameworks for simplified module management and configuration.
- Perform unit testing to verify individual module functionality and interactions.
- Document the module interface clearly, including input parameters, output values, and expected behaviors.
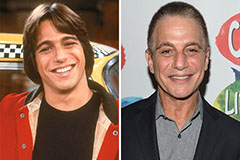 Tony Danza Then & Now!
Tony Danza Then & Now! Judge Reinhold Then & Now!
Judge Reinhold Then & Now! Freddie Prinze Jr. Then & Now!
Freddie Prinze Jr. Then & Now! Andrew McCarthy Then & Now!
Andrew McCarthy Then & Now! Katey Sagal Then & Now!
Katey Sagal Then & Now!